Cyber criminals increasingly favouring ‘low and slow’ stealth attacks
A “low and slow” approach to financially driven cyber attacks has overtaken ransomware as the chief attack vector as criminals seek to extort money by stealth using crypto mining-based malware, according to research from vendor Darktrace
A “low and slow” approach to financially driven cyber attacks has overtaken ransomware as the chief attack vector for criminals seeking to extort money by stealth using crypto mining-based malware, according to research by British cybersecurity upstart Darktrace.
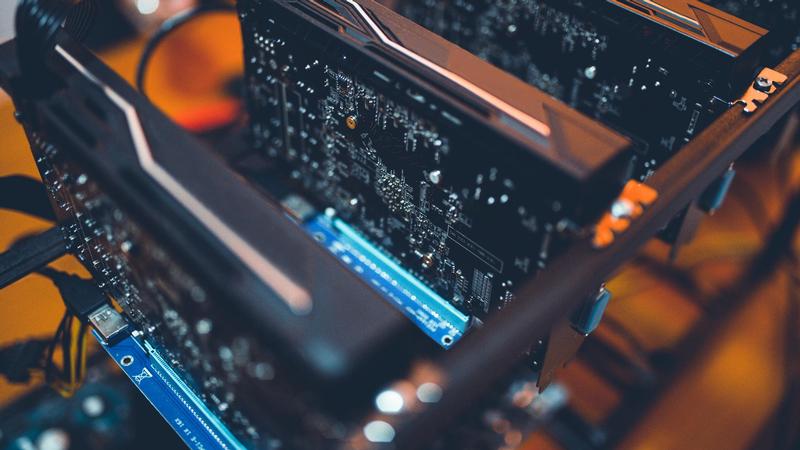
Although ransomware made headlines when it wrought havoc across the UK, Europe and America, most prominently with WannaCry, a new generation of malware is instead sitting quietly on users’ devices and in data centres to steal electricity and bandwidth to mine crypto currencies such as Monero
According to Darktrace, throughout 2018 and into 2019 there had been increasing prominence of malware with crypto mining payloads, as well as the return of banking trojans.
Speaking with Computerworld UK, director of threat hunting at the company Max Heinemeyer, said that Darktrace had seen “very creative forms of crypto jacking going on”. Speculating as to why this shift was taking place, he said that it’s possible threat actors lost profit because ransomware victims may not have been tech-savvy enough to actually go onto Tor and make bitcoin payments.
“A better approach might be to go underground and use crypto mining because it is low and slow and guarantees a profit,” he said.
Heinemeyer said that the company had even seen one attacker, who was a system admin at a major European bank, install a mining device underneath the floorboards of the data centre he worked at to use the capacity of his workplace to mine currency.
And a company in the UK was hit by a crypto mining variant that spread laterally through the organisation within minutes of the initial spear phishing email, where the trojan had spread to more than 400 devices within the environment.
“We’ve seen crypto mining malware that isn’t running at full capacity to avoid overheating computers and making the fan spin at 100 percent, to avoid these physical implications of being very loud,” he said.
Unlike bitcoin, Monero is relatively easy to mine on commodity hardware – so it’s easier to mine the currency on a run of the mill laptop and therefore more profitable.
“We’ve seen so many different variants of how these pieces of malware are spreading or being loaded it’s fair to say there are a lot of players in the crypto mining market, and the barriers to entry to creating your own crypto mining malware is rather simple these days,” he said.
Credit card fraud is “cumbersome” because in order to avoid alerting law enforcement immediately, the criminals have to establish money laundering networks where intermediaries might buy luxury goods with the stolen data. Ransomware was “another nice way to monetise” and now crypto currency mining is “yet another tool in their arsenal”, as Heinemeyer put it.
While crypto mining might not be as obviously damaging to a victim, they’re just as dangerous as other attacks because once a machine is compromised other back doors could be established and, for example, turn into a credit card trojan later.
“So there’s still a huge risk to it besides the obvious electricity and computing power that’s being stolen,” Heinemeyer said.
Case study: CCTV gone wild
The new report is tied in to the launch of Darktrace’s new Antigena ‘cyber AI response modules’, and also included some examples of attacks that the vendor had seen.
Antigena modules extend beyond the internal network of an organisation and into the public cloud (specifically AWS and Azure) as well as Office 365 and other software-as-a-service applications.
The company found that at a Japanese investment consultancy, an internet-connected CCTV system had been compromised – meaning they could watch the entirety of the office including the CEO’s office and the boardroom.
However, the company claims that its algorithms picked up unusual behaviour on the unencrypted CCTV server, with large volumes of data moving out to an unknown web address. Here, Antigena blocked data movement from the device to external servers while allowing the camera to operate as it was intended to.
“Most legacy security tools wouldn’t catch this because they would say, ‘I don’t have a rule for this’ – a CCTV camera gone rogue,” said Heinemeyer. “Our AI fights back autonomously instead of waiting for the human to confirm this, look into this and research this, because the data is going out there right now, our AI stops the traffic and says instead of this one CCTV camera going rogue we’re going to enforce what all the other CCTV cameras do.
“So normal operations are going to be enforced, and only the weird behaviour is going to be stopped. So the data exfiltration was stopped but the CCTV camera could still be used by the internal CCTV team.”
Source : https://www.computerworlduk.com
Stay ahead with ITBusinessNews – Your trusted source for Technology and Business news. Fast & Precise





